Microsoft Teams Phone System
Did you know Microsoft offer a cloud based phone system? Integrated within your Office 365 system, a fully cloud based phone system means no paying for onsite hardware and you can handle landline calls from anywhere on any device you have a mobile data/internet connection. The phone functionality is built on the Microsoft Teams platform, so as well as using Teams for your company collaboration and team work, it can also provide you a fully functioning office phone system. With so many businesses now choosing to allow their staff to work from home, a cloud based phone system means you never really have to be 'out of the office'.
- Get started from as little as £7.50 per month/per user
- Optional calling plans to suit business needs
- No reliability on office hardware/internet connections
- Completely cloud based
- Works with existing handsets (based on model)
- No hardware means reduced maintenance overheads
- Familiar interface for staff provides easy adoption
- Make calls directly from your Outlook contacts
- Compatible with mobile devices
- Simple to use


Office 365 'Voicemail' Phishing
The latest phishing attempt appearing in people's inboxes consists of an email notifying you that you have a new voicemail message in your 'Office 365 Voicemail' system. The screenshot to the right shows an example of one of the emails. Here are some things to look out for to tell if this email is a scam:
- The obvious one first - if you are not aware of an Office 365 voicemail system in use then you won't have a voicemail to listen to.
- The 'play' button in the email is purely an image, the hope is that you will click the button and it will take you to a malicious website. Hover over links first to see where they are directing you to.
- The email sender will try to impersonate someone legitimate in the business, in our example, the attacker has tried to make the email look like it has come from our helpdesk.
- Check the sender address (next to the sender's name), the email will likely be sent from an address that is not legitimate and clearly has no link to the supposed name of the sender.
- Watch out for logos/icons that you do not recognise in the email. This example has a logo that is not recognisable and is clearly not Microsoft branded.
Microsoft offer additional email security features and tools in Office 365, speak to one of the team to find out more about how you can protect your business when opening emails.
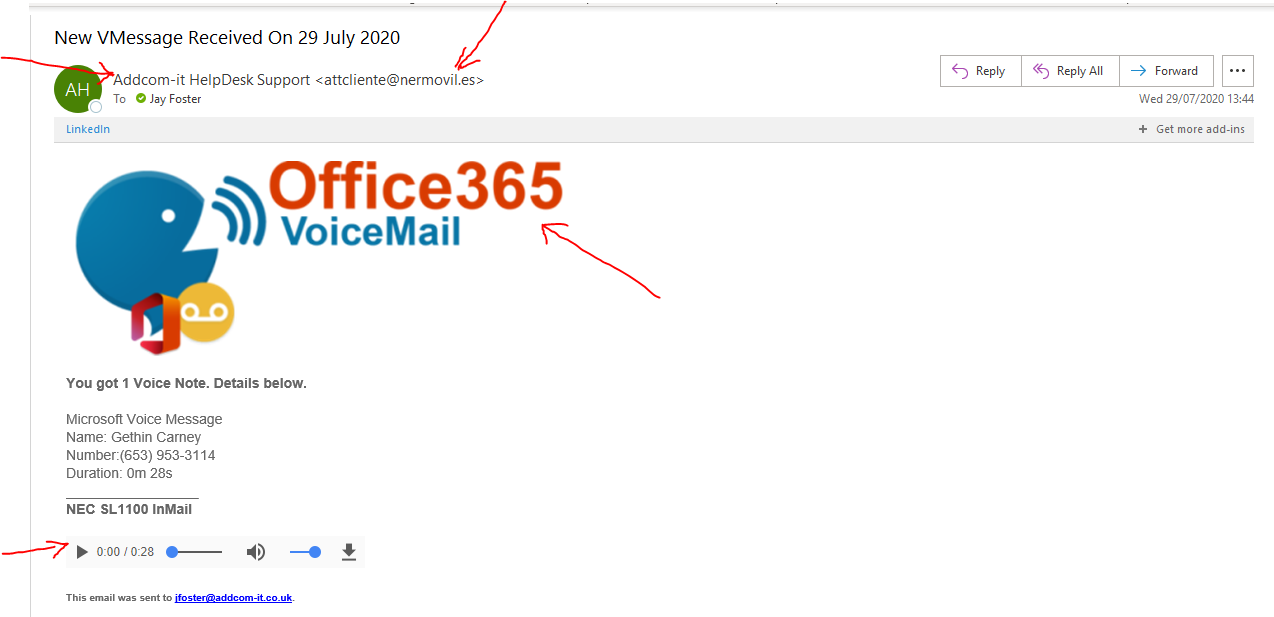
An example of a current phishing email being sent to businesses.
Work quicker with these keyboard shortcuts
Keyboard shortcuts help get things done quicker and more efficiently, check out some of the most useful Windows shortcuts below:
- CTRL + A = Highlight all text/images on the page.Great if you want to delete lots of text in one go and copy to another application.
- CTRL + C = Copies the text you have highlighted. The quicker alternative to right clicking and clicking 'copy'.
- CTRL + V = This pastes what you have copied, so this works great with CTRL + C...especially as they are next to one another on the keyboard!
- CTRL + Z = Undo, this will undo any action you have just carried out, such as a paste or a deletion of text
There are lots of different useful shortcuts available, let us know below in the comments section if there are any in particular that you find useful or use regularly!